PHP Malware C99 Shell
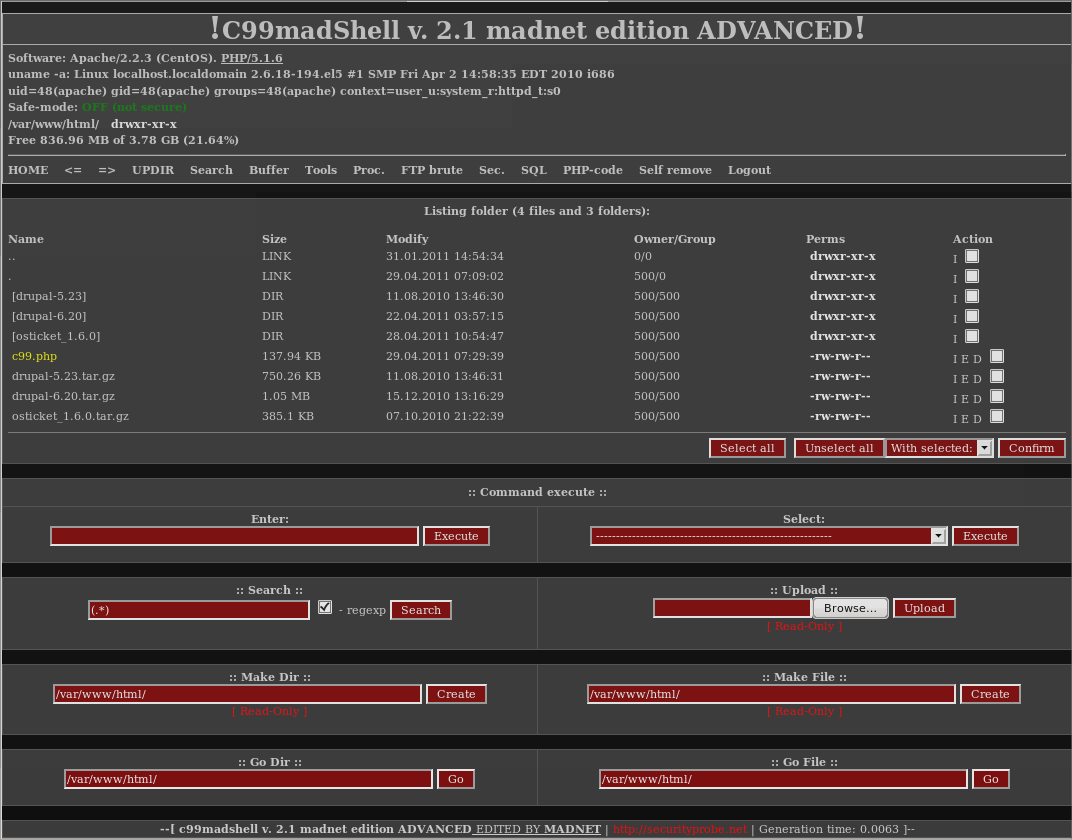
The c99 shell is a somewhat notorious piece of PHP malware. C99 shell is often uploaded to a compromised web application to provide an interface to an attacker. The c99 shell allows an attacker to hijack the web server process, allowing the attacker to issue commands on the server as the account under which PHP is running. The c99 shell allows an attacker to browse the filesystem, upload, view, and edit files as well as move files, delete files, and even change permissions, all as the web server. Finding the c99 shell on your system is pretty solid evidence of a compromise.
Luckily, if you find the c99 shell on your system, you can usually recreate much of the attack using log files. If the attacker never manages to gain root access every request to c99 will be logged as a normal web request. Because c99 uses GET URL variables for many of its options so it is possible to recreate an attackers footprints by looking through web server access logs. Unfortunately many of the operations within c99 utilize arguments passed via form posts, which are not logged, and so you may not be able to find a complete command history.
There are several versions of c99 shell floating around online. This is a relatively recent version, culled form an incident response (i.e. in the wild). Feel free to take a look, there are many signatures in the file that can be used to write defensive countermeasures.
The c99 shell can be found here. I've tried to post the actual code, but at over 2,500 lines it's not very manageable via a web browser.