Madirish Tutorial 11 (Brute Forcing)
This article is designed to demonstrate how to accomplish a brute force attack, and what it looks like from the receiving end. Brute force means password guessing. This can only feasibly be accomplished with the aid of good target reconnaissance and some automated programs. While it is very easy to write your own brute force program, there are several available for free online. I find Brutus to be one of the best brute force tools. You can find it at Hoobie.net.
The first step in a brute force attack (or for that matter, any attack) is target enumeration. This is the process by which we find where and how a target is vulnerable. I use NMAP for almost all of my initial cursory scans of networks. Lets use the target of my own desktop server and run an NMAP scan to find out what we have to play with. The output from my scan follows:
nmap -sS -O 216.25.200.135 Starting nmap V. 2.30BETA17 by fyodor@insecure.org (
www.insecure.org/nmap/ ) Interesting ports on ip-216-25-200-135.covad.dsl.fcc.net
(216.25.200.135): Port State Service 21/tcp open ftp 25/tcp open smtp 80/tcp open http 135/tcp open loc-srv 139/tcp open netbios-ssn 443/tcp open https 445/tcp open microsoft-ds 1025/tcp open listen 1026/tcp open nterm 1031/tcp open iad2 TCP Sequence Prediction: Class=random positive increments Difficulty=7635 (Worthy challenge) Remote operating system guess: Windows 2000 RC1 through final release Nmap run completed -- 1 IP address (1 host up) scanned in 1 second
Ok, so we’ve got several services to choose from on this target. The first one that catches my eye is FTP. We can use this to brute force passwords, and we can use smtp to check for user accounts. Now the fun begins. I’ll first try ftp to find if anonymous ftp is enabled (which could potentially make my task a lot easier, there are rare computers with completely open upload/download ftp servers without strong restrictions (allowing you to upload and download to the web root folder)).
C:\>ftp 216.25.200.135 Connected to 216.25.200.135. 220 WIN2KSERVER Microsoft FTP Service (Version 5.0). User (216.25.200.135:(none)): anonymous 331 Password required for anonymous. Password:foo@nowhere.com 530 User anonymous cannot log in. Login failed. ftp> quit 221 Fuck off!
It seems that anonymous ftp isn’t enabled, and not only that the server is quite rude when I leave. The server did give some confirmation that it is running Windows NT, or in this case Windows 2000 (dead giveaway in the machine’s name ‘WIN2KSERVER’). We’ll try the SMTP server now to check for user names.
220 WIN2KSERVER Microsoft ESMTP MAIL Service, Version: 5.0.2195.2966 ready at Fri, 22 Jun 2001 09:08:49 –0400 vrfy smellydell 252 2.1.5 Cannot VRFY user, but will take message for smellydell vrfy administrator 252 2.1.5 Cannot VRFY user, but will take message for administrator
well, there’s no use in verifying anyone on this server as it seems that the server will give the same message for real and bogus accounts (all NT servers have an ‘administrator’ account, in much the same way that *nix have root accounts). The ‘expn’ command didn’t work at all on this server (replied with ‘unknown command’ at expn postmaster). So at this point I’m SOL, but some machines will give a very good list of users and or active accounts using the smtp server.
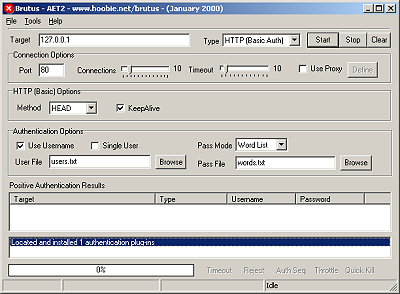
Ok, so I’m off to brute forcing. The first thing I do is fire up Brutus.
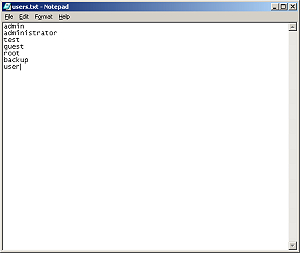
Next I’ll have to modify my users list (found in users.txt in the Brutus directory) to include users I suspect to be on an NT server. NT always has a ‘Guest’ account and an ‘Administrator’ account. I’ll add a few more guesses. In the end my users list looks like this:
The next step is to fire Brutus at the target, when configured for an ftp attack, Brutus appears thus:
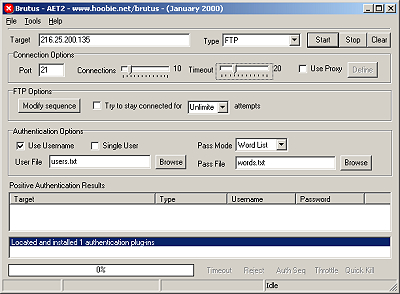
You’ll notice I set the timeout higher than the default. Brutus nicely circumvents connection limits by creating new connections for every request. This is useful because some servers will cut your connection after 3 bad guesses at passwords. Brutus uses the targets ability to take multiple ftp requests and creates a new request for every guess (I have set the program to make 10 requests simultaneously). The timeout is the lag time that the program will allow before it makes a new request. If you don’t set this high enough you are likely to flood the target and either crash its server, or simply hang Brutus. You can use a really high connection and low timeout rate as an effective DoS attack that will knock weak servers completely off the net.
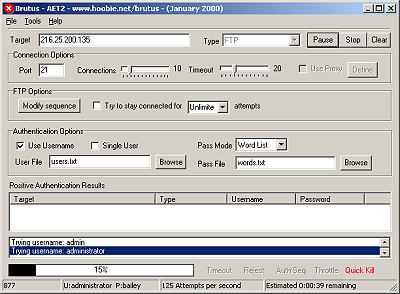
So now I’ll fire Brutus at the target. I’m using the default password list that comes with the program, but there are several larger, and more complete word lists available online. What Brutus will do is try every username listed in the users file with every password in the word list (and can even generate its own random word list to include all combinations of letters, characters, and numbers). Remember that most passwords are 8 characters long, so its usually not worthwhile to try and brute force very short passwords. Here’s what Brutus looks like in action:
Now, the downside to brute forcing is that it is extremely noisy, and even the worst sysadmin should notice it. During my demonstration my server immediately popped an alert that the system log was full. A quick examination of the system log reveals the problem immediately:
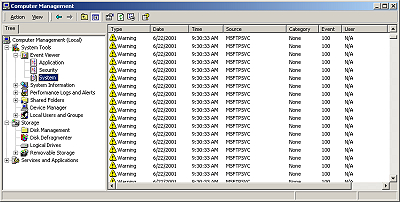
All those warnings you see are bad FTP login attempts. A double click on the alert shows:
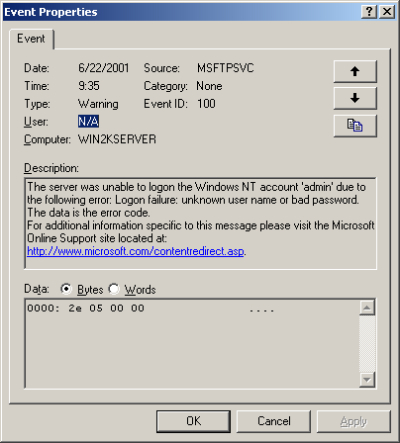
It isn’t hard to figure out exactly what is going on. Even more disturbing is the log file left behind. Here’s a snippit:
13:30:18 216.25.200.135 [5]USER admin 331 13:30:18 216.25.200.135 [6]USER admin 331 13:30:18 216.25.200.135 [7]USER admin 331 13:30:18 216.25.200.135 [8]USER admin 331 13:30:18 216.25.200.135 [9]USER admin 331 13:30:18 216.25.200.135 [10]USER admin 331 13:30:18 216.25.200.135 [11]USER admin 331 13:30:18 216.25.200.135 [12]USER admin 331 13:30:18 216.25.200.135 [13]USER admin 331 13:30:18 216.25.200.135 [4]PASS - 530 13:30:18 216.25.200.135 [14]USER admin 331 13:30:18 216.25.200.135 [5]PASS - 530 13:30:18 216.25.200.135 [6]PASS - 530 13:30:18 216.25.200.135 [7]PASS - 530 13:30:18 216.25.200.135 [8]PASS - 530 13:30:18 216.25.200.135 [9]PASS - 530 13:30:18 216.25.200.135 [10]PASS - 530 13:30:18 216.25.200.135 [11]PASS - 530 13:30:18 216.25.200.135 [15]USER admin 331 13:30:18 216.25.200.135 [16]USER admin 331
Not only do you notice all the tries for the same account, but you can tell it is an automated attempt to brute force because the times of the attempts are so close together (60 or so attempts a second). Even more damning is that my IP address is logged all over the huge log file. Its not hard to spot me or figure out what I’m attempting to do. Be warned if you attempt a brute force that you are probably going to get notice.
Now, I happened to be successful on this attempt and got on username and password. The results are displayed in Brutus under the ‘Positive Authentication Results’ window:
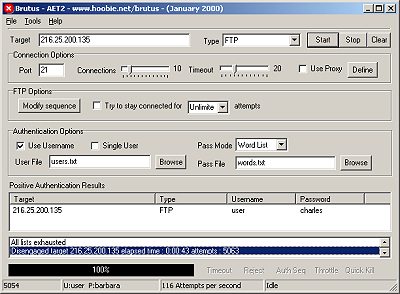
You can see the username ‘user’ and password ‘charles’ worked on the server. Lets try them out:
C:\>ftp 216.25.200.135 Connected to 216.25.200.135. 220 WIN2KSERVER Microsoft FTP Service (Version 5.0). User (216.25.200.135:(none)): user 331 Password required for user. Password: charles 230-Fuck you! 230 User user logged in. ftp>
Boom, and its just that easy. Now that I’m in my first step should be to attempt to clean up the traces of my attack (i.e. the log files and system event logs). Accomplishing this task takes more explanation than I have time for here, but hopefully you get the idea.
If nothing else, this short article should show you the value of good passwords. If I hadn’t set up the account ‘user’ with such a crappy password this attack most likely would have been unsuccessful. See my article on passwords for a good run down of how to pick a good password to keep your accounts safe from brute force attempts.